End-to-end Cybersecurity with aiXDR
Stay Vigilant, Stay Ahead of Your Adversaries.
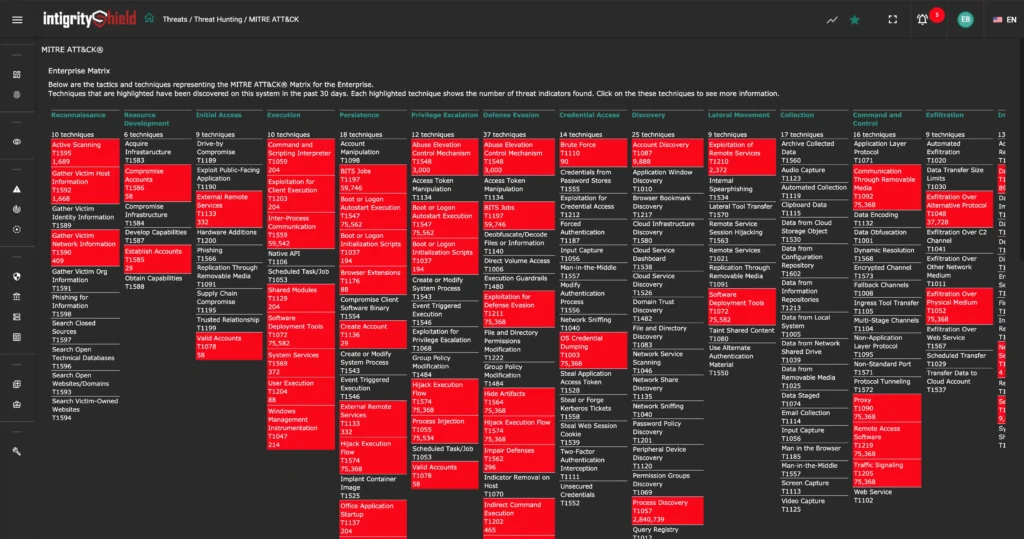
When it comes to safeguarding digital information, IT assets, and business data, IT organizations often struggle with a quasi-normal state due to the lack of comprehensive insights from endpoints, servers, firewalls, user and entity behaviors, network traffic, vulnerabilities, and threat intelligence. Secure your critical frontiers—whether remote, in the cloud, in the office, or in transit—with intigrityshield aiXDR. Leverage insights from razor-sharp analytics, powered by AI and ML.

In the evolving landscape of remote work and sophisticated attacks, any weakness can be exploited by adversaries. Common vulnerabilities include:
- Malware downloaded from malicious websites or spam emails
- Compromised credentials of endpoint users through brute-force attacks
- Unmonitored use of VPN browsing to access torrent files
- Data leakage of business and privacy-protected information by employees
- Use of public Wi-Fi for business applications involving sensitive data
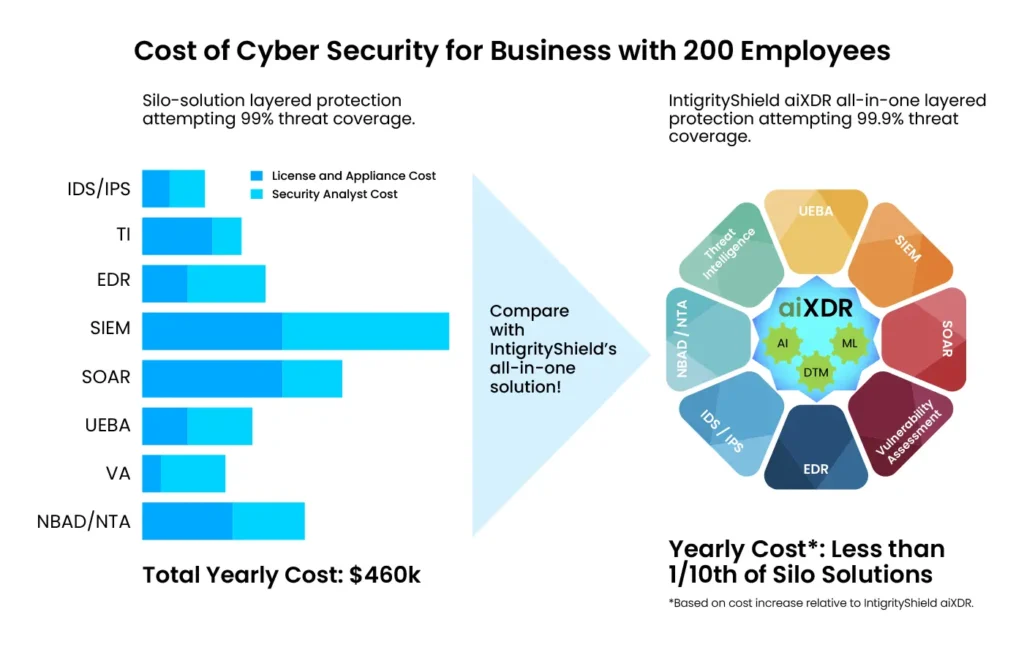
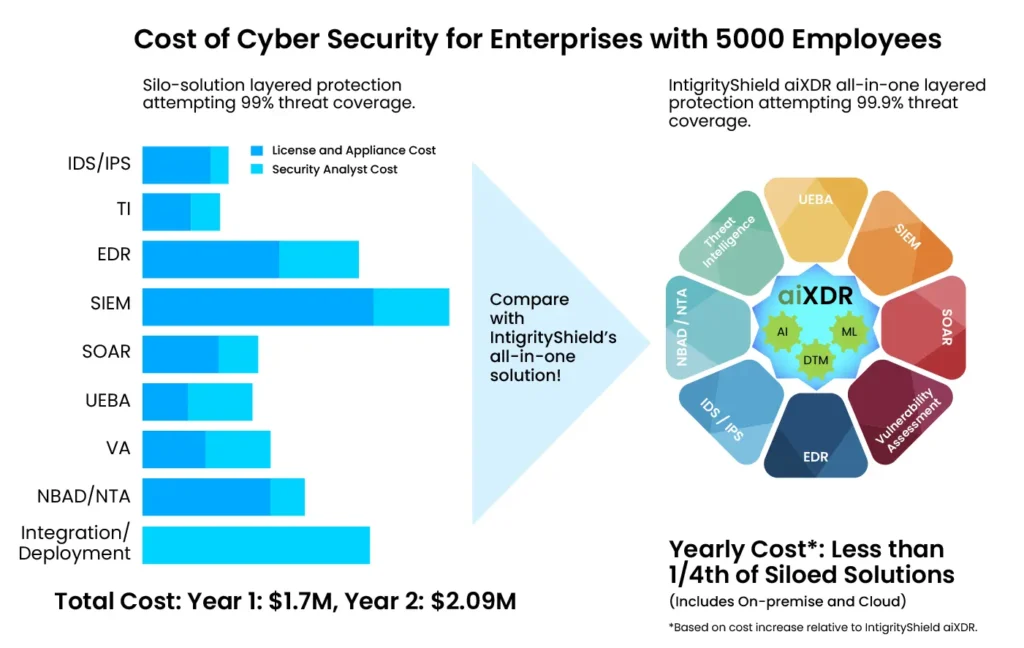
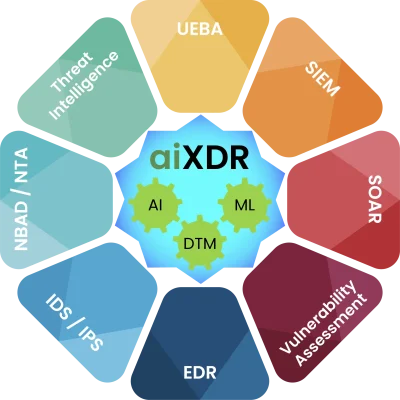
Relying solely on a particular layered protection, such as EDR, IDS/IPS, SIEM, SOAR, or Network Security, will not provide sufficient coverage for the critical assets your business relies on. intigrityshield’s aiXDR integrates all these protective layers, organically built with real-time analytics, defense-in-depth oversight, and dynamically adaptive threat models powered by Artificial Intelligence.
intigrityshield’s aiXDR eliminates uncertainty and gaps in the cybersecurity landscape, offering a comprehensive "One Stop Shop" for multi-layered protection against threats, attacks, compromises, and exploits.
Comprehensive Security For Your Digital Assets
Rest assured with assimilated threat indicators across IT, OT and IoT, contextually enriched with Threat Intelligence, Behavioral Anomalies and Vulnerability Assessment.
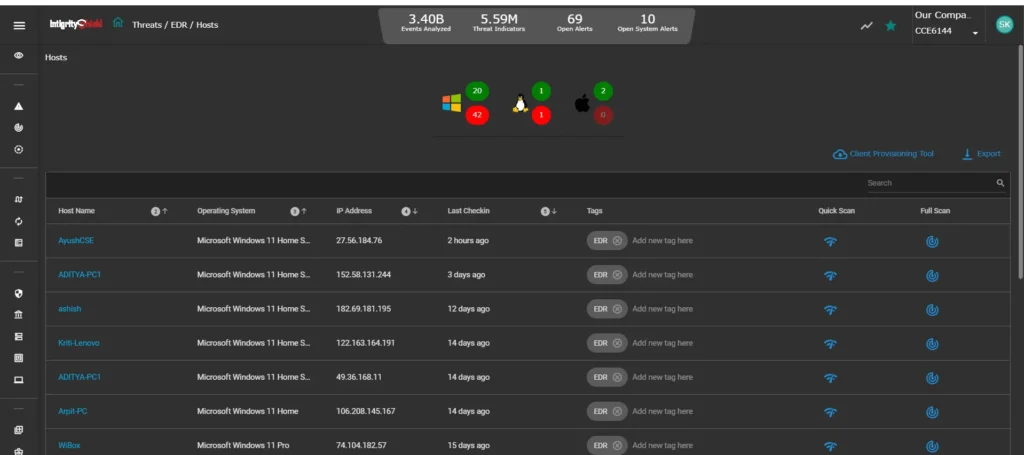
Rich and Pertinent Evidence Derived From Various Sources
Uncover evidences of suspicious process, harmful executable, evasive tactics, recon activities and more through combination of lightweight agents and agentless technologys.
Powerful AI, ML And DTM To Preempt Incidents
Reap the benefits of Machine Learning, Artificial Intelligence and Dynamic Threat Models as alerts are generated preemptively with confidence scores.
Product Feature Comparison